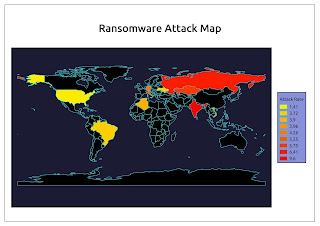
Using GIS software to develop a cyber map for analysis of cyber attacks globally helps IT security understand cyber world and to identify vulnerabilities in cyber networks which allow security teams to prioritize their work and solve areas with the potential to do the most damage first.
Below are some cyber map images develop with GIS software.
The accuracy of the data is not guaranteed and mostly referenced to the work of Cyber Security Insides on the following link.
https://www.cybersecurity-insiders.com/list-of-countries-which-are-most-vulnerable-to-cyber-attacks/
http://gis.usc.edu/blog/gis-and-cybersecurity/


pm me
ReplyDelete